Checkpoint Harmony Network Security
Highest Level of Security for Remote Users

Overview
Harmonize Security for Users, Devices & Access
Best Prevention. Simple for Everyone.
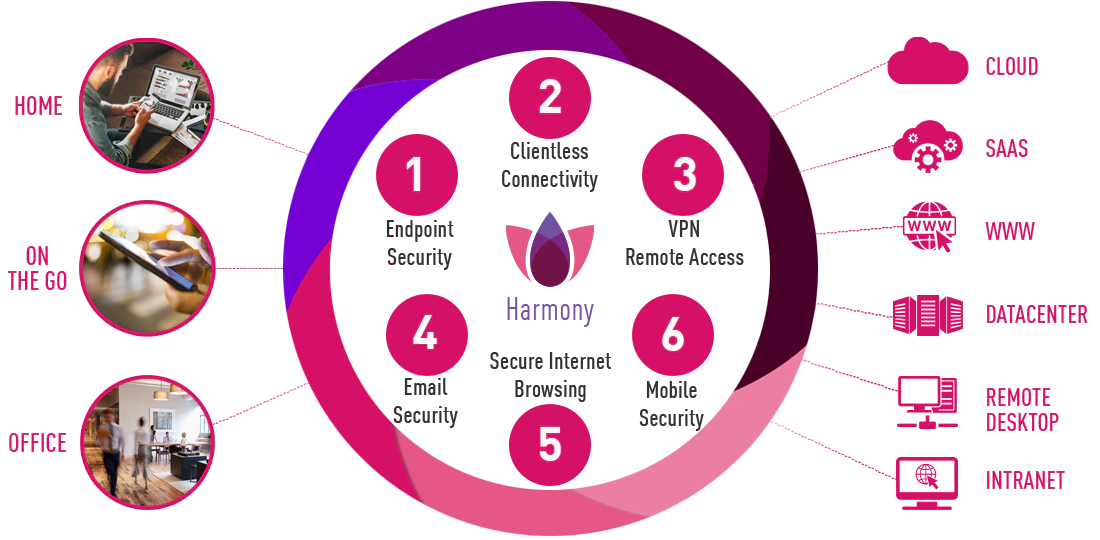
Protecting today’s hyper-distributed workspace requires endless security functions across user devices, applications and networks. However, stitching together point solutions often leaves security gaps and creates a cumbersome infrastructure that is difficult to manage and scale. Harmony offers an alternative that saves you the overhead and increases security.
Key Benefits
Maintain Productivity While Staying Protected, in Everything You Do
Harmony unifies 6 cloud-based security products to keep you 100% safe. Wherever you connect from, whatever you connect to, and however you connect – Your home, your devices, your privacy and your organizational data are secured and protected from any cyber threat.
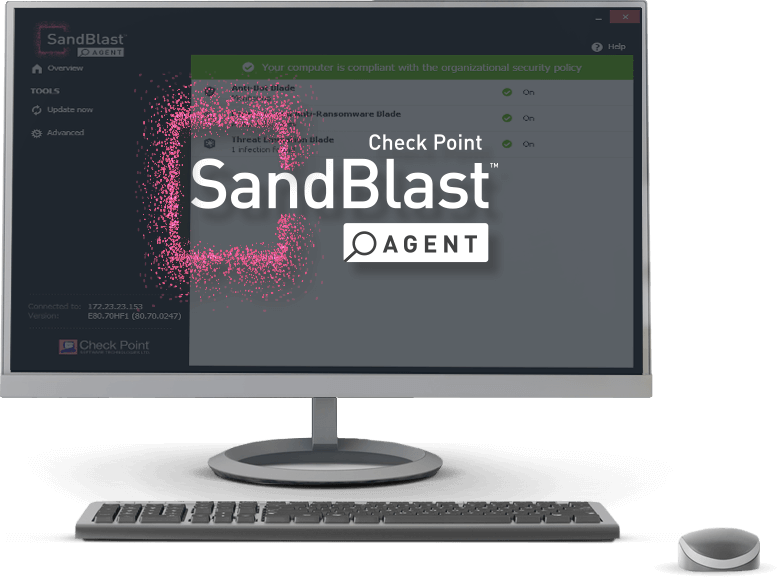
Endpoint Security
A complete endpoint security solution built to protect user PCs and laptops from today’s complex threat landscape.
- Full Endpoint Protection from the most imminent threats such as ransomware, phishing, and malware
- Fastest recovery to enable quickly minimize breach impact with autonomous detection and response.
Advanced Endpoint Threat Prevention
Extends zero-day protections to both endpoints & web browsers. Endpoints are protected with Threat Emulation, Threat Extraction & Anti-Ransomware.
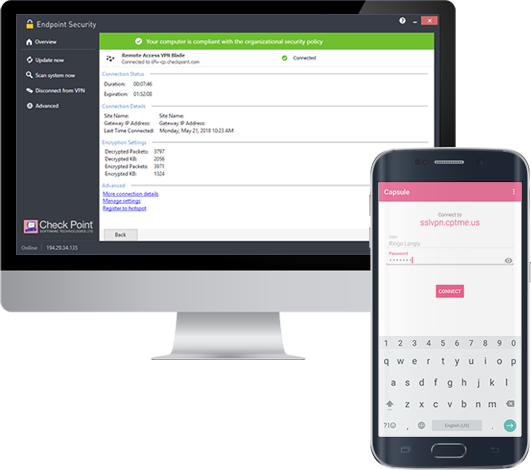
Remote Access VPN
Check Point Remote Access VPN provides users with secure, seamless access to corporate networks and resources through multi-factor authentication, compliance scanning and encryption.
Mobile Security
Keep your corporate data safe by securing employees’ mobile devices across all attack vectors: apps, network and OS. Perfectly fits into your existing mobile environment, deploys and scales quickly, and protects devices without impacting user experience nor privacy.
Mobile Threat Defense
Check Point SandBlast Mobile protects iOS and Android devices from advanced mobile threats, ensuring you can deploy and defend devices with confidence.
Mobile Secure Workspace
Capsule Workspace provides a secure business environment for mobile device use and protects business documents wherever they go.