Check Point CloudGuard Workload Protection
Check Point CloudGuard Workload Protection
Contact us for Pricing!
Get a Quote
- Container Inventory
- Traffic Visibility and Investigation with Log.ic
- Compliance for Containers
- CloudBots for Cloud Native Containers
- Continuous Vulnerability Scanning & Assessment
Overview:
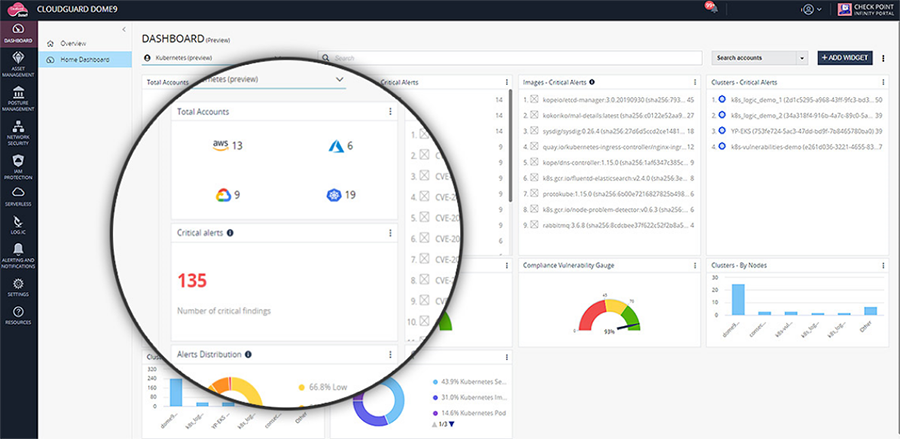
Check Point CloudGuard Workload Protection, part of the CloudGuard Cloud Native Security platform, provides seamless vulnerability assessment, and delivers full protection of modern cloud workloads, including serverless functions and containers, from code to runtime – automating security with minimal overhead.
![]()
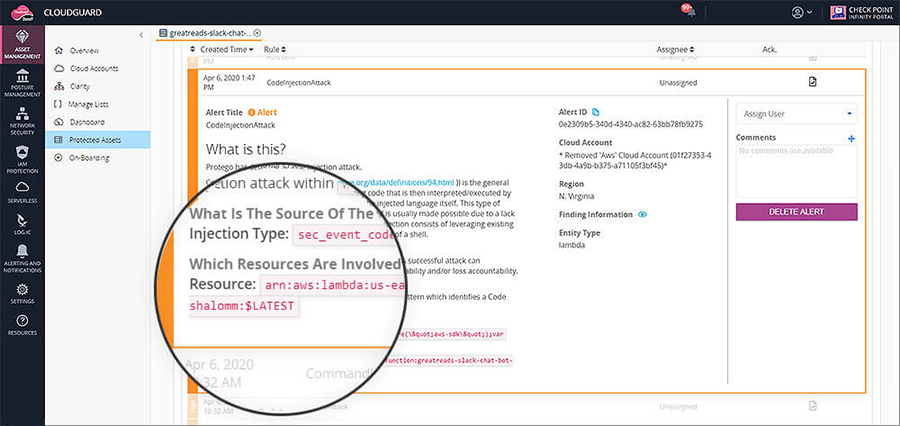
Security Scanning and Analysis
Detect over-permissive roles, vulnerabilities, and embedded threats
![]()
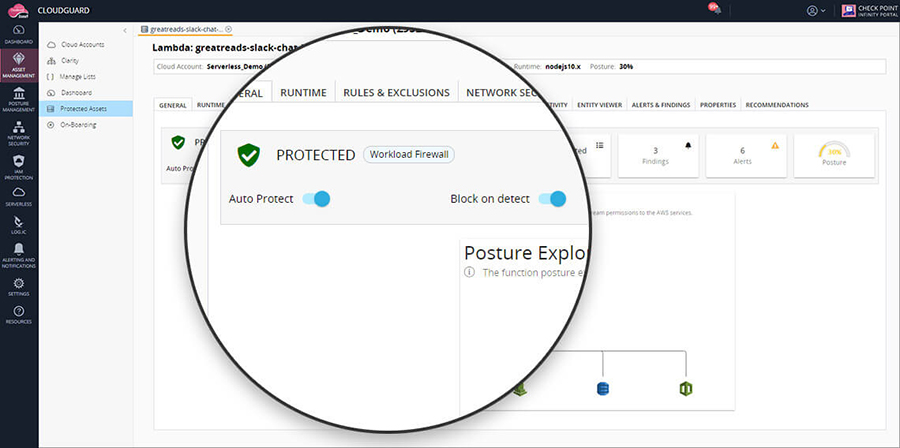
Automated Runtime Protection
Multi layer security, leveraging machine learning to profile and protect workloads
![]()
Governance and DevSecOps
Enforce granular security policies during CI/CD and production for all workloads
Automated Workload Protection
Check Point CloudGuard Workload Protection capability provides a comprehensive solution for automating security for the most demanding modern architectures- offering observability, least privilege protection, and active threat prevention across serverless, containers, and other microservices.
Workload Protection
Modern cloud-native application security, needs to be built from the ground-up with the inner workings of the application in mind. Traditional application security protocols simply do not work alone with these modern architectures as the mechanic of the application has fundamentally changed. Organizations need to reimagine the way AppSec is done without negatively affecting the operational benefits of these modern workloads like efficiency, cost savings, etc.
From development through production, Check Point CloudGuard automates workload protection and offers continuous cloud security posture management and compliance with customizable policies (using GSL) across accounts. Only CloudGuard offers:
- Observability: Continuously scan your serverless functions, to increase security posture- providing clear observersability of the application and continuous assessment.
- Least Privilege Protection: Maximize workload protection through automatic least privilege protection for containers, logs, and databases.
- Active Threat Prevention: Zero-touch application security using pattern matching, whitelisting, blacklisting, and more applied at the function level for threat prevention.
Pricing Notes:
- Pricing and product availability subject to change without notice.